Although browsing the online, some end users have found a popup information indicating Your personal computer has been compromised or hacked. Diverse customers have viewed this information on distinctive browsers, including Chrome, Firefox, Edge, and so on. Immediately after receiving this warning concept, the afflicted people scanned their pcs with the antivirus set up on their devices but the antivirus did not obtain any risk. If the antivirus threat report is apparent, what does this concept signify? Is this information serious or faux? In this post, we will see what the Your laptop or computer has been compromised or hacked message usually means and what you should do if you see this information on your laptop or computer.

Your computer has been compromised or hacked
According to the responses of the impacted users, their web browser refuses to near after they receive the popup message. Also, a call number is shown together with the warning concept. When they contacted that number, the assist individual questioned them for some cash to deal with the challenge. On the other hand, some buyers have also claimed that immediately after visiting a certain net web page, in its place of the warning popup message, they heard a voice declaring “Your Personal computer is hacked.”
Some users were being also advised to give accessibility to their desktops in buy to take care of the problem. This is a spam and deceptive concept. You should disregard it in any other case, you will develop into the prey of hackers. Moreover, if you grant accessibility to your computer system to the particular person on the phone, he/she could steal the data saved on your laptop that may possibly include sensitive details.
These types of types of warning messages normally screen either a call selection or a connection. We suggest you do not click on the website link exhibited in these kinds of forms of warning messages. If you do so, a virus or malware may perhaps enter your method and may perhaps start off sending your facts to the hackers. Or, clicking on that connection might set up a method on your program. That software may perhaps consist of a suspicious code. These forms of malicious applications are intended to adjust the registry keys on a user’s computer.
If you see a Your personal computer has been compromised or hacked warning information while surfing the web, you need to consider the pursuing steps straight away in get to shield your personal computer from malware or virus an infection:
- Disconnect your World-wide-web connection
- Close your web browser
- Scan your process with antimalware
- Update your website browser
- Remove unwelcome extensions
- Delete your browser cache or reset your browser
- Uninstall the not too long ago mounted courses
- Operate SFC and DISM scans
Beneath, we have described all these steps in depth.
1] Disconnect your World wide web link
Straight away disconnect your World-wide-web relationship very first.
2] Near your world wide web browser
The future point that you should do is to near your website browser. But in accordance to the people, the popup information could stop you from closing the world-wide-web browser. If these a point transpires to you, stick to the underneath-mentioned methods to near your website browser:
- Press the Ctrl + Change + Esc keys to launch the Job Manager.
- When the Task Manager appears on your display screen, pick the Procedures tab.
- You will see your web browser less than the Applications part. Appropriate-simply click on your website browser and choose Stop Undertaking.
If the above approach fails, pressure shut down your laptop or computer by pressing and keeping the electric power button and then transform it on.
3] Scan your technique with antimalware
If you have clicked on the backlink delivered in the warning information or if you have granted obtain to your pc to the person on simply call, there is a potent probability that your computer has been contaminated by a virus. Run a complete program antivirus scan.
Browse: How do you convey to if your computer system has a virus?
4] Update your internet browser

Launch your web browser and near all the opened tabs if any.
Now update your internet browser. It is proposed to generally use the latest variation of the software in purchase to prevent glitches. If you use the latest model of the world wide web browser, the likelihood of obtaining a virus or malware attack grow to be much less.
Read through: On the internet Fraud in Cyber crime: Prevention, Detection, Restoration
5] Remove undesirable extensions

Now, the following move is to get rid of unwanted extensions from your web browser. Extensions make our work simpler on a world wide web browser. From time to time, extensions bring about difficulties. If you have clicked on the website link exhibited in the warning information, it is doable that an extension is installed on your browser with no your information. For this reason, it is important to examine if there is any unwanted extension put in on your browser. If you uncover any unwanted extension or an extension that is installed on your net browser without your information, take out it straight away.
Go through: Malware Removing Tutorial & Equipment for Beginners.
6] Delete your browser cache or reset your browser
You must also delete your browsing history, which include the cookie and cache info. Press the Ctrl + Change + Delete keys to open the Obvious Browsing Facts window in your website browser. This shortcut functions with most world-wide-web browsers. When the Distinct Browsing Details window seems, pick out cookies, cache, and browsing background. In the time range, pick out All Time. If you want to delete your saved passwords, you can also do that.
Alternatively, you could want to look at resetting your browser to default point out to be incredibly protected.The measures to reset some well-known web browsers are stated down below:
- To reset or refresh Mozilla Firefox, open up its options and go to “Help > Troubleshooting Info.” Now, click on on the Refresh Firefox button.
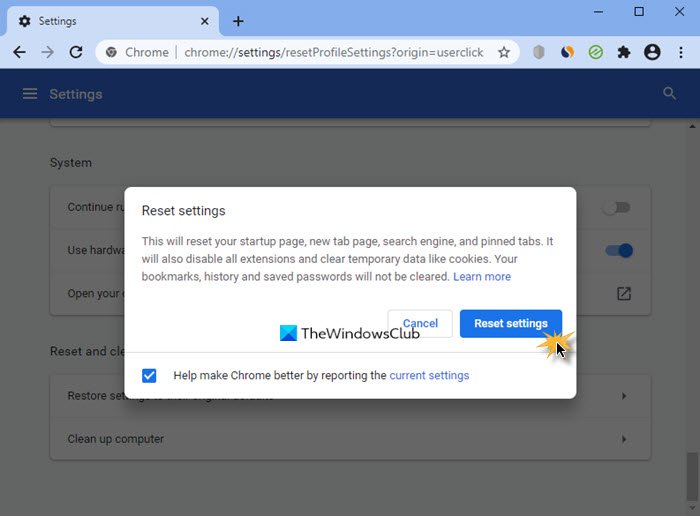
- To reset Google Chrome, open up its configurations and go to Superior Options. Now, click on on the Restore options to their primary defaults button.
- To reset Microsoft Edge, open up its settings and then simply click on the Reset Options alternative on the still left pane.
7] Uninstall the not long ago put in applications
If you have named the scammers or clicked on the connection displayed in the warning message, the scammers may have mounted a plan on your system. Open up the Apps & Features page in Windows 11/10 Options and see if there is any not long ago set up application. If of course, uninstall it immediately. The pursuing methods will tutorial you on how to do that.

- Open up Home windows 11/10 Settings.
- Go to “Apps > Applications & Features.”
- Form all the mounted applications by day. For this, select Date set up in the Form by fall-down.
- See if there is any plan that is set up without having your expertise. If certainly, uninstall it.
8] Operate SFC and DISM scans
It is also doable that some of your program graphic data files are broken because of to malware or virus an infection. To verify this, operate an SFC scan. SFC stands for Technique File Checker. It is an automated software developed by Microsoft that checks for destroyed or corrupted program graphic files and repairs them (if doable).
We also suggest you run a DISM scan on your program. The DISM or Deployment Image Servicing and Management is a command-line resource. Like SFC, it also repairs the corrupted or harmed technique graphic data files. It is usually made use of when SFC fails to restore the procedure impression files.
Study: What to do right after a Ransomware attack on your Windows personal computer?
What does it indicate if your personal computer is compromised?
A compromised pc is a laptop or computer, the confidentiality of which is adversely impacted, either deliberately or unintentionally. The phrase Compromised laptop or computer is commonly applied for hacked computer systems. There are a lot of methods by which hackers can hack your process. The most frequent way is the phishing try. The phishing makes an attempt are ordinarily performed by sending an email to the consumer with some suspicious links. When a consumer clicks on these back links, he will be redirected to the site that seems specifically the similar as the official web site. These internet sites trick users and they enter their confidential data although signing in. In this way, hackers steal the private details of the consumers.
When surfing the internet by using your internet browser, some of you could possibly have witnessed the messages very similar to the pursuing kinds soon after checking out some precise websites:
- Your laptop may well be at possibility. Run a no cost antivirus scan to protect your computer system.
- Virus detected. Run a free antivirus scan to get rid of the virus from your laptop or computer.
Such types of sites are malicious internet websites. Clicking on any of the one-way links on such internet sites installs malware on the user’s pc. Soon after the malware is set up, a destructive code is executed on his/her computer system and the hacker is in a position to steal the information and facts from the contaminated computer. Some malware are also able of changing the registry keys on a Windows laptop or computer.
Tip: Secure yourself, stay clear of online ripoffs and know when to trust a web site!
Does Microsoft simply call you about your pc staying hacked?
Maintain in thoughts that neither Microsoft nor its partners call you for your computer system protection difficulties. You want to master how to discover frauds that fraudulently use the Microsoft identify. The motive of these phone calls is to steal the confidential info from the user’s laptop so that they could use it for blackmailing purposes. The man or woman on simply call may perhaps also check with to obtain your computer system by installing a particular software program. If you grant him/her accessibility to your laptop, he/she may well execute a destructive code on your system or entirely lock your laptop or computer. Immediately after that, the hacker will check with you for a specific quantity of revenue to unlock your computer system.
Hope this can help.
Examine future: Command and Management Cyberattacks: How to Recognize and Protect against them?






More Stories
Quantum Space picks up speed with $15M in funding for cislunar space vehicles • TechCrunch
Tender Alerts: What They Are and How They Can Benefit Your Business
The Next Global Economic Revolution